iSpy: The CIA Campaign to Steal Apple’s Secrets
Researchers working with the Central Intelligence Agency have conducted a multi-year, sustained effort to break the security of Apple’s iPhones and iPads.
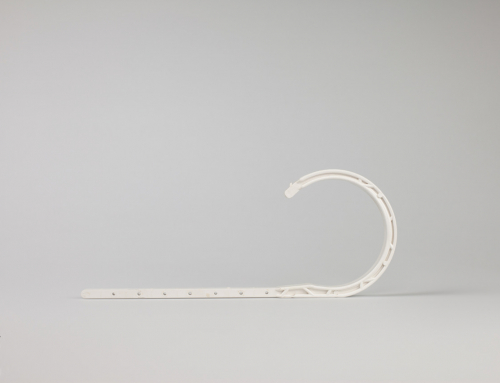
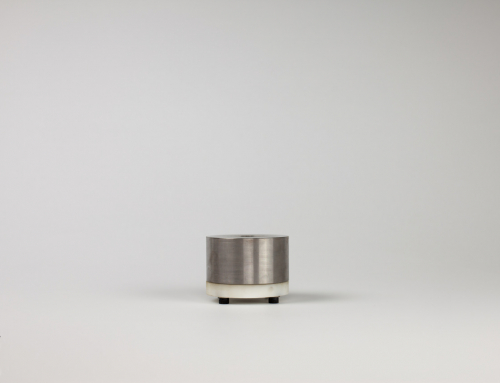
At the 2011 Jamboree conference, there were two separate presentations on hacking the GID key on Apple’s processors. One was focused on non-invasively obtaining it by studying the electromagnetic emissions of — and the amount of power used by — the iPhone’s processor while encryption is being performed. Careful analysis of that information could be used to extract the encryption key. Such a tactic is known as a “side channel” attack. The second focused on a “method to physically extract the GID key.”Whatever method the CIA and its partners use, by extracting the GID — which is implanted on the processors of all Apple mobile devices — the CIA and its allies could be able to decrypt the firmware that runs on the iPhone and other mobile devices. This would allow them to seek out other security vulnerabilities to exploit. Taken together, the documents make clear that researching each new Apple processor and mobile device, and studying them for potential security flaws, is a priority for the CIA.
I’m not really shocked by security stories anymore, but I would tip my hat to them for figuring this out if it wasn’t so terrifying. The “fragmented” landscape of Android is a feature when you’re facing a situation like this.